Y-Wing Chains
This strategy has been deprecated. It is a clear subset of other chaining strategies and does not need to be identified uniquely
Our pivot chain for a Y-Wing must proceed at odd numbered cells (or even number of links). A Y-Wing is simply a chain with length = 1.
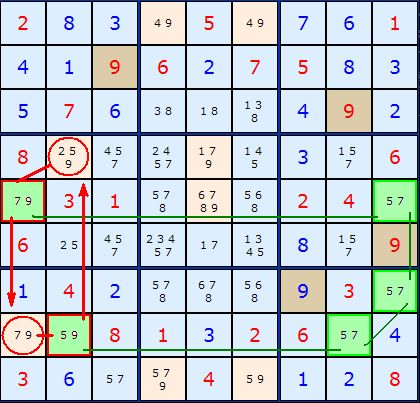
In Figure 1 we have a Y-Wing Chain marked out in green cells. The 5/7 pivot consists of three pairs of 5/7. The first 5/7 (in which ever order) is connected to the last 5/7 by a third 5/7 in the middle, and by definition this is a locked pair. If the first 5/7 is a 5 then the third one must be a 5 as well. Same goes for number 7.
Our pincer is based on the two green cells marked with a red border - the pairs 7/9 and 5/9. The principle of the Y-Wing says that any cells that both those can see we can eliminate the common number - in this case 9. The two cells marked with a red circle can be 'seen' by both and the 9 removed.

Comments
Email addresses are never displayed, but they are required to confirm your comments. When you enter your name and email address, you'll be sent a link to confirm your comment. Line breaks and paragraphs are automatically converted - no need to use <p> or <br> tags.
... by: Donald
Thanks